Insights
Welcome to the Black Belt Secure cybersecurity blog, your trusted source for the latest cybersecurity insights, news, and best practices in the ever-evolving world of digital security. Here, you’ll find a wealth of information covering everything from emerging threats and vulnerabilities to practical tips and strategies for protecting your business. Our cybersecurity blog is dedicated to empowering individuals and organizations with the knowledge they need to navigate the complex cybersecurity landscape and stay one step ahead of cybercriminals.
Categories
Knocking on Your Office Door: The FBI Warns of Silent Ransom Group Stealing Data In Person
by Team Black Belt | May 29, 2026 | Cybercrime
The Silent Ransom Group is behind a dangerous new threat where, after phishing emails and phone calls fail, they send a physical operative straight to your office. They walk past the front desk and plug a flash drive directly into an employee’s computer to steal data....
The Fall of a “Bulletproof Hosting” Giant: What the Dutch Server Takedown Teaches Us About Infrastructure Risk
by Team Black Belt | May 28, 2026 | Network & Infrastructure
In a major blow to state-sponsored cyber operations, Dutch financial crime investigators (FIOD) recently executed a massive raid, arresting two individuals and seizing more than 800 servers. This significant operation targeted bulletproof hosting providers—including...
Shai-Hulud Worm Clones Hit NPM: New Supply Chain Attacks Emerge Days After Source Code Release
by Team Black Belt | May 22, 2026 | Cybersecurity News
We’ve spoken on this before but it seems that the open-source software ecosystem never sleeps—and neither do the attackers targeting it. Just days after the source code for the notorious Shai-Hulud worm was publicly released on GitHub, copycat threat actors have...
Microsoft Exchange Server Zero-Day Under Active Exploitation: What Businesses Need to Do Now (CVE-2026-42897)
by Team Black Belt | May 20, 2026 | Cybersecurity News
In the world of cybersecurity, Exchange Server zero-day vulnerabilities are among the most dangerous threats IT leaders face today. On May 14, 2026, Microsoft disclosed a high-severity Exchange Server zero-day (CVE-2026-42897) that is already being actively exploited...
AI Zero-Day Exploit: AI Just Wrote Its First Zero-Day Exploit — And It Nearly Pulled Off a Mass Attack
by Team Black Belt | May 12, 2026 | Artificial Intelligence, Cybersecurity News
The cybersecurity community has been debating for years whether AI would eventually be weaponized to discover and exploit vulnerabilities at scale. As of today, that debate is over. Google's Threat Intelligence Group (GTIG) has published findings confirming what many...
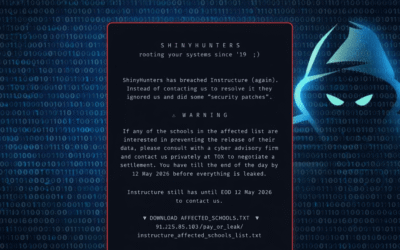
ShinyHunters Canvas Breach: Group Hits Instructure Twice in One Week — What Schools and Businesses Must Know
by Team Black Belt | May 12, 2026 | Cybercrime
When a cybercrime group hacks your platform, publicly embarrasses you, and then does it again just days later — that’s not bad luck. That’s a systemic failure. That’s exactly what happened in the ShinyHunters Canvas breach. Instructure, the company behind Canvas — one...
AI Security Flaws Far More Severe Than Traditional Bugs: New Pen Test Data Reveals the Risks
by Team Black Belt | May 12, 2026 | Artificial Intelligence, Cybersecurity News
In a striking new report, AI security flaws are proving significantly more dangerous than traditional software vulnerabilities. According to Cobalt’s 2026 State of Pentesting Report, 32% of findings in AI and LLM systems were rated high-risk — nearly 2.5 times higher...
ShinyHunters Canvas Breach: Hackers Deface 330 School Portals in Escalating Extortion Attack
by Team Black Belt | May 12, 2026 | Cybersecurity News
In a major ShinyHunters Canvas breach, the notorious extortion group has defaced login pages of approximately 330 educational institutions using Instructure’s Canvas platform. The attackers are demanding ransom and threatening to leak 275 million student records by...
Why Your Next Microsoft Teams Message Could Be a Microsoft Teams Phishing Threat
by Team Black Belt | Apr 23, 2026 | Cybercrime
For years, organizations have trained employees to spot phishing attempts in their email inboxes. But as internal communications move toward platforms like Microsoft Teams, attackers are now aggressively following suit. A new "enterprise intrusion playbook" has...
Critical Alert: CISA Warns of Active Exploitation in Cisco Catalyst SD-WAN
by Team Black Belt | Apr 23, 2026 | Cybersecurity News
In the world of enterprise connectivity, addressing a Cisco Catalyst SD-WAN vulnerability is now a top priority for security teams. SD-WAN (Software-Defined Wide Area Network) serves as the backbone of the modern distributed enterprise, but recent disclosures from...
Payroll Pirates: The Rising Cyber Threat Stealing Employee Paychecks
by Team Black Belt | Apr 16, 2026 | Cybercrime
Have you heard of payroll pirates? There’s a new term making the rounds in cybersecurity circles — and if you haven’t heard it yet, you need to. Payroll pirates are cybercriminals who don’t bother breaking into your bank account directly. Instead, they hijack your...
Iranian Hacking Campaign Picking Up Steam: Iranian Hackers Targeting PLCs
by Team Black Belt | Apr 15, 2026 | Cybersecurity News
Iranian hackers targeting PLCs are ramping up their cyberattacks against U.S. critical infrastructure — and the scale of exposure is alarming. A newly issued joint advisory from the FBI, CISA, NSA, the Environmental Protection Agency (EPA), the Department of Energy...

Co Founder and Vice President
Peter Vavrosky, a cybersecurity expert with over 20 years of experience in infrastructure and network engineering, co-founded Black Belt Secure in 2020, transforming it into one of North Texas’ most acclaimed cybersecurity firms, recognized with multiple national awards. His work securing critical systems and designing tailored solutions for SMBs highlights his commitment to digital safety. As a university educator, Peter also shapes the next generation of cybersecurity professionals, while his speaking engagements across DFW inspire businesses to prioritize robust security. Read Peter’s full profile for more details.
Read More