When a cybercrime group hacks your platform, publicly embarrasses you, and then does it again just days later — that’s not bad luck. That’s a systemic failure.
That’s exactly what happened in the ShinyHunters Canvas breach. Instructure, the company behind Canvas — one of the world’s most widely used learning management systems — suffered two major security incidents within a single week. If your school, university, or business uses Canvas or any third-party SaaS platform, this incident carries important lessons for you.
What Happened
The trouble began on May 1, 2026, when the cybercrime group ShinyHunters claimed responsibility for breaching Instructure’s systems. They alleged they had stolen data linked to roughly 8,809 schools, universities, and education platforms — impacting an estimated 275–280 million individuals. The stolen data reportedly included usernames, email addresses, student ID numbers, private messages, enrollment records, and information accessed through Canvas data export features and APIs.
Instructure acknowledged the breach and declared it “contained” the following day.
It was not.
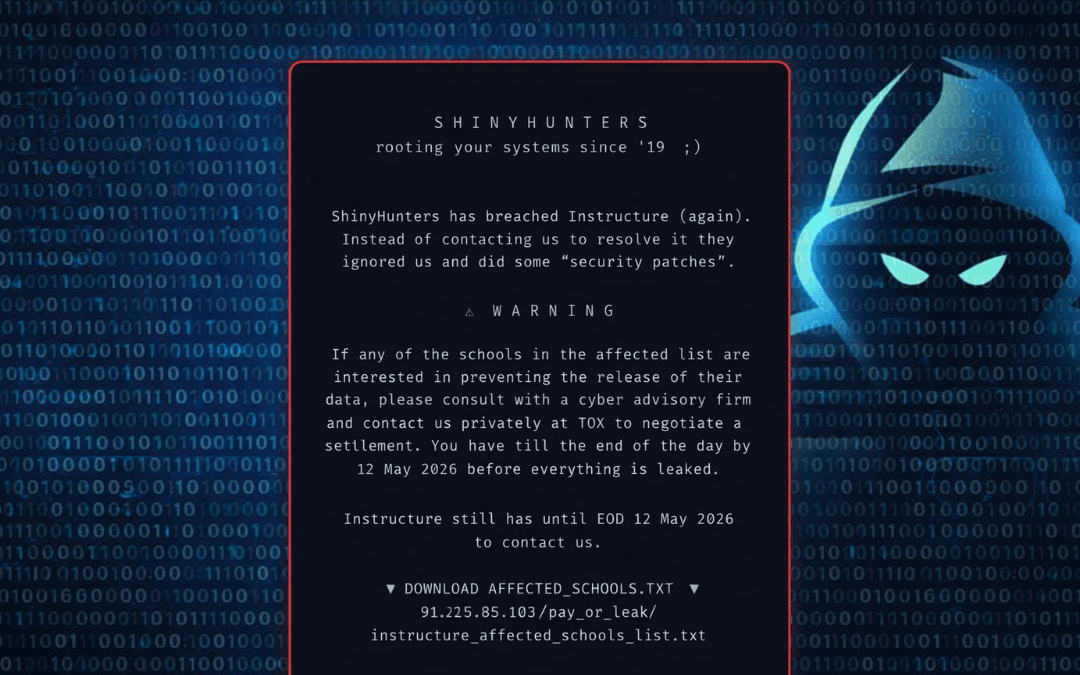
On May 7, just six days later, Canvas login portals for an estimated 330 colleges and universities were defaced. Students at institutions including Columbia, Princeton, Harvard, Georgetown, the University of Michigan, the University of Washington, and Baylor University saw a message from ShinyHunters instead of their coursework:
“ShinyHunters has breached Instructure (again). Instead of contacting us to resolve it, they ignored us and did some ‘security patches.’”
The attackers threatened to leak all stolen data by May 12 unless schools negotiated a ransom. The defacements lasted roughly 30 minutes before Instructure took Canvas offline. Upon restoring service, the company confirmed the attackers had exploited the same vulnerability tied to Free-For-Teacher accounts that enabled the original breach.
Why the ShinyHunters Canvas Breach Matters to Every Business
Canvas powers more than 30 million active users across over 8,000 institutions worldwide. While this is primarily an education-sector story, the ShinyHunters Canvas breach carries critical implications for all organizations that rely on third-party SaaS platforms.
- Third-Party Risk Is Your Risk
Your organization doesn’t need to be the direct target. ShinyHunters reportedly used Canvas as an initial foothold into the University of Pennsylvania’s systems as early as September 2025 — eight months before the public incidents. - “Contained” Doesn’t Mean Fixed
Instructure’s leadership declared the May 1 breach contained. Six days later, ShinyHunters proved them wrong on a global stage using the exact same vulnerability. This highlights the dangerous gap between public statements and actual remediation. - Free or Freemium Tiers Are a Hidden Attack Surface
The vulnerability was linked to Instructure’s Free-For-Teacher accounts, which typically have lighter security controls. Many SaaS platforms share infrastructure between free and paid tiers — meaning their risk becomes your risk. - Extortion Has Evolved
ShinyHunters didn’t just demand ransom privately. They publicly defaced hundreds of login portals, timed the attack for finals week, and used media pressure to maximize leverage. This is the new standard extortion playbook.
The Attack Pattern Security Experts Are Flagging
Security researchers noted this was not a spontaneous attack but a calculated escalation:
- September 2025: Initial access gained via Canvas into University of Pennsylvania systems
- May 1, 2026: Large-scale breach claimed; Instructure declares containment
- May 7, 2026: Public defacement proves containment failed
This pattern — quiet reconnaissance, failed containment, public shaming, and extortion — is becoming common among sophisticated groups like ShinyHunters.
What Schools and Organizations Should Do Right Now
For Canvas Users:
- Be vigilant for phishing emails impersonating Canvas
- Assume your institution’s email addresses, usernames, and IDs may be compromised
- Alert students and staff to heightened social engineering risks
- Rely only on official communications from your institution
For IT and Security Teams:
- Audit all free and freemium SaaS tiers in use
- Strengthen vendor risk management and demand clear incident response SLAs
- Maintain communication plans that do not depend on third-party platforms
- Review API integrations and data export permissions
For Leadership and Boards:
- Require detailed root cause analysis from vendors — not just “contained” statements
- Verify cyber insurance coverage for third-party SaaS disruptions
- Treat third-party risk management as a board-level priority
The Bigger Picture
The ShinyHunters Canvas breach is a textbook case of why third-party risk management can no longer be treated as optional. Organizations that blindly trust vendor assurances without verification are exposing themselves to significant danger.
Threat actors are patient. ShinyHunters reportedly maintained access for eight months before striking. The warning signs were there — they were just quiet.
At Black Belt Secure, we help organizations close these exact gaps through comprehensive vendor risk assessments, third-party access audits, and proactive threat intelligence.
Don’t wait for a defaced login page to discover your exposure.
Concerned about your organization’s third-party risk exposure?
Schedule a consultation with our team — we’ll help you see what your vendors aren’t telling you.